Effective access is what a user or system can actually do across your environment—based on all permissions, roles, OAuth grants, service accounts, and app-level access.
It is not what your identity provider says should exist.
It is what actually exists.
Most companies assume their identity provider is the source of truth for access.
It isn’t.
Your IDP controls who can log in. It does not control everything they can do after that.
Real access lives in:
That creates two versions of access:
Those two drift apart constantly.
Bob moves from Engineering to Sales Engineering.
In your IDP:
Looks correct.
But in reality:
His intended access changed.
His effective access didn’t.
Because access is fragmented across systems.
Each system manages its own permissions:
Identity providers were built to handle authentication and group-based access.
They were not built to continuously track everything happening inside every system.
They are the front door, not the control room.
If you only look at intended access, you miss the real risks:
Most gaps do not happen at login.
They happen after login.
To understand effective access, you need to:
Effective access is the actual set of permissions a user or system has across all systems, including apps, OAuth connections, and service accounts.
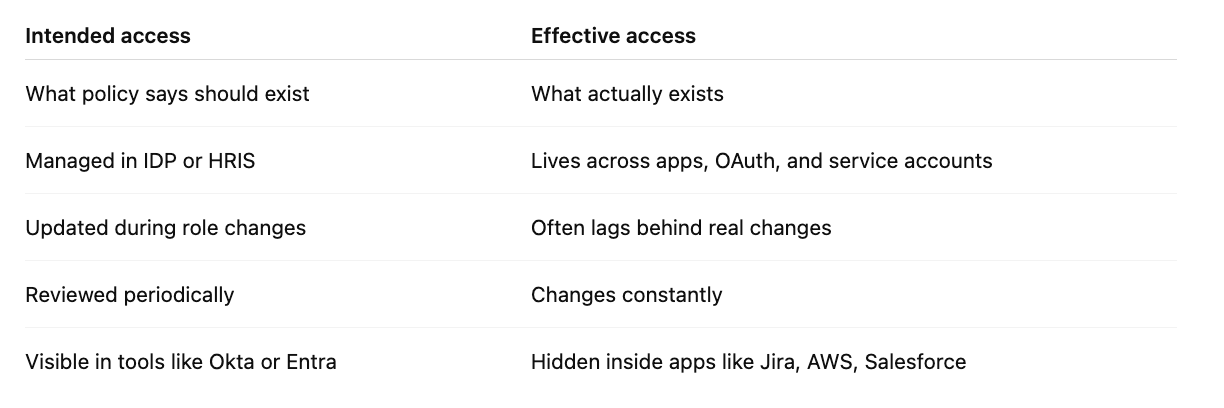
Intended access is what policies define. Effective access is what exists in reality across systems.
Because most access is managed inside applications, OAuth connections, and service accounts—not in the IDP itself.
Users retaining admin access after role changes, OAuth apps accessing sensitive data, service accounts with excessive permissions, and permissions managed directly inside apps.
You need to connect to the systems where access lives, aggregate permissions, and continuously monitor changes across those systems.
YeshID is built around effective access.
Instead of relying on what your IDP says should exist, YeshID connects directly to the systems where access actually lives and shows you what’s real.
So you can:
If your security model stops at login, you’re missing most of the picture.
Effective access is the full picture.